Pivoting is, in my humble opinion, the most important skill of intrusion analysis and incident response. I have been teaching/training/mentoring intrusion analysts for over 7 years. In my experience, this is the most difficult skill to train as it requires creativity, attention to detail, and a full knowledge of their data sources and how to exploit those.
Pivoting is the ability to identify a critical piece of information and being able to maximally exploit that information across all of your sources to substantially increase your knowledge of the adversary and further identify the next critical piece of information – which is then pivoted upon moving you deeper into the operation of the adversary – hopefully earlier into the kill-chain.
An example: trolling through log files you discover a very odd HTTP user-agent accessing your website. You then query on this user-agent across all the log entries and identify a significant number of users providing this string value. (Pivot on user-agent) You then extract all of those particular log entries and identify a regular time pattern of access indicating automated functionality. You also discover that all the requests have a very odd resource/page request – bob.php. (Pivot on bob.php) You then take that page name (bob.php) and examine all HTTP traffic in your network over the last 2 days and discover that several hosts in your network have been POSTing odd data to bob.php….at this point you may retrieve and conduct a forensic analysis on the hosts, etc. When you finally discover that the adversary has compromised several internal hosts and has had them HTTP POSTing data to a webpage on your external-facing website of which the adversary then uses to extract the information/data. At this point, you now have several pieces of mitigative value: the source IP of the adversary’s infrastructure on the outside, the page deposited on your website, any malicious tools discovered on the hosts, the HTTP traffic, etc. All of which are collectively more valuable to defense than any one of those pieces of information independently.
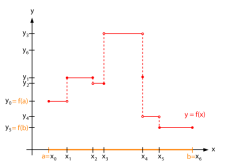
In this way, analysis and incident response is a step-function. Most of the time analysis is, in a sense, rote. It involves looking through log files, examining and validating alerts, looking at various binaries. Step by step peeling back the onion of the adversary’s operations. At times we even move backwards as an analyst makes an incorrect assumption or a poor hypothesis which costs time/money/resources to recover and correct the analytic path. However, when a piece of critical information is discovered it should be exploited and a deeper knowledge should be achieved moving the analysis to a “new level” of the function substantially increasing the knowledge as a whole – which, in theory, should lead to additional mitigative opportunities.
My favorite analogy is that of the game of “Chutes and Ladders” (or “Snakes and Ladders” for those outside the US). A player slowly moves across the board block-by-block but then happens on a ladder which moves them up substantially in the board. Other times, they land on a snake/chute which then brings them back down. This is the process of analysis.
Why does this matter? It matters because this understanding can help us better understand the process and model of analysis thereby providing an opportunity for researchers to target parts of analysis to increase the chances/likelihood of a step-function increase in knowledge and decrease the chance of a decrease.
One way is to increase the capability of analytic tools to maximize pivoting. Allowing for an easy and quick way to query other data sources with a new discovery and integrating that into the analytic picture. The tools should also allow an analyst to ‘back-up’ their analysis removing a possible poor path once an error is discovered.
This is just a couple of ideas. I’d love to hear yours.